TLDR: HIPAA compliance ensures patient data is handled safely across healthcare operations, including customer service. By understanding PHI, knowing who must comply, following core HIPAA rules, and adopting secure processes and systems, healthcare organizations can reduce compliance risks, prevent data breaches, and build lasting patient trust.
Protecting patient data is a foundational requirement for any healthcare organization, and HIPAA compliance plays a central role in ensuring that customer service operations handle sensitive information securely.
From appointment inquiries to billing support and medical record requests, every customer interaction may involve health information.
Without the right systems and safeguards in place, even routine support activities can put patient privacy and organizational compliance at risk.
To meet these standards, healthcare teams must rely on well‑defined policies, trusted technologies, and consistent practices that protect patient’s information at every stage.
A recent study by DialogHealth reveals that 99% of businesses view HIPAA compliance as a critical component of their operational strategy.
This guide explains HIPAA compliance in healthcare requirements, outlines actionable steps, and demonstrates how compliance strengthens customer trust and operational efficiency.
What does HIPAA compliance mean?
HIPAA compliance means protecting patients’ sensitive health information by following the requirements of the Health Insurance Portability and Accountability Act.
It is especially important in customer support workflows where patients’ information is frequently exchanged.
To stay compliant, organizations must:
- Establish clear internal policies and procedures
- Train employees on proper PHI handling
- Monitor system access and activity
- Regularly review and update security and compliance practices
A HIPAA-compliant help desk supports these requirements by ensuring that patient information is handled securely and in accordance with regulatory standards.
What is Protected Health Information (PHI)?
Protected Health Information (PHI) is any information that can identify a person and is linked to their health, medical care, or payment for healthcare under HIPAA.
PHI can exist in electronic, paper, or verbal form. Common examples of PHI include:
- Names, addresses, phone numbers, and email addresses
- Dates such as birth, admission, discharge, or death
- Photographs and full-face images
- Social Security numbers and medical record numbers
- Health plan and account numbers
- Any unique identifier connected to health-related information
When personal or demographic details are combined with health-related data, the information becomes PHI and must be protected.
Even a support ticket created to track the request must be handled according to HIPAA safeguards.
Who needs to be HIPAA compliant?
HIPAA applies to covered entities and their business associates that handle PHI during healthcare transactions or support processes.
Covered entities
Covered entities are organizations that electronically transmit health information during transactions governed by standards adopted by the U.S. Department of Health and Human Services.
These covered entities fall into three distinct categories, each playing a critical role in managing and transmitting protected patient health information securely.
- Health plans: Health insurance companies, HMOs, Medicare, and Medicaid.
- Healthcare providers: Doctors, clinics, hospitals, psychologists, dentists, chiropractors, pharmacies, and nursing homes that conduct certain transactions electronically.
- Healthcare clearinghouses: Entities that process nonstandard health information they receive from another entity into a standard format.
Business associates
Business associates refer to individuals or entities performing services or functions for covered entities that involve using or disclosing protected patients health information responsibly.
Examples of business associates include:
- External medical billing companies.
- Data storage and cloud-based system providers.
- Attorneys, accountants, and consultants who handle PHI.
- HIPAA-compliant software vendors (like a secure help desk platform).
Covered Entities and Business Associates must have a BAA. This Business Associate Agreement is a required contract that ensures the Business Associate safeguards PHI.
4 HIPAA rules and regulations you must know
With the basics covered, let’s explore HIPAA-compliance main rules. Understanding these helps organizations protect health data and stay compliant across all healthcare operations and digital environments.
A report by Security Metrics indicates that 81% of the 100 surveyed healthcare organizations encrypt patient data in accordance with HIPAA regulations.

HIPAA privacy rule
The HIPAA Privacy Rule governs how PHI can be used and shared while giving patients control over their personal health information.
- Individuals can view records, request updates, and track who accessed their medical information over time.
- Organizations must share only essential data needed to complete a specific task or fulfill a defined purpose.
- Clear privacy notices must explain how healthcare providers use, store, and disclose sensitive patient information.
HIPAA security rule
The HIPAA Security Rule focuses on safeguarding electronic protected health information (ePHI) through administrative, physical, and technical controls.
- Administrative safeguards include assigning roles, training staff, and creating policies to manage digital security risks.
- Physical safeguards involve securing buildings, devices, and systems from theft, damage, or environmental hazards.
- Technical safeguards use encryption, access controls, and monitoring tools to protect data during storage and transmission.
HIPAA breach notification rule
The HIPAA Breach Notification Rule requires organizations to notify affected individuals and authorities when unsecured PHI is exposed.
- Notifications must describe the incident, what information was exposed, and how people can protect themselves.
- Small-scale breaches follow annual reporting, while larger incidents require immediate disclosure.
- Entities have 60 days to notify after discovering any unauthorized data exposure.
HIPAA omnibus rule
The HIPAA Omnibus Rule strengthens enforcement, expands patient rights, and extends compliance obligations to business associates and subcontractors.
- Business associates and subcontractors must now follow HIPAA rules and report any data breaches.
- Patients can request digital copies of records and limit sharing with insurers when paying privately.
- Privacy policies must reflect updated rights, marketing limits, and breach response procedures.
You can learn more directly from the U.S. Department of Health and Human Services by reviewing the HIPAA Privacy Rule, HIPAA Security Rule, and HIPAA Breach Notification Rule.
Meeting HIPAA security standards reduces the risk of data breaches, unauthorized access, and costly compliance violations especially in customer service environments that handle PHI daily.
7 elements of an efficient HIPAA-compliance program
An efficient HIPAA-compliance program provides a clear structure for protecting patient information and maintaining consistent adherence to regulatory requirements.
It outlines the key practices organizations must follow to manage PHI securely, reduce compliance risks, and ensure every process aligns with HIPAA standards.
- Written policies and procedures: Create clear documentation that defines responsibilities and support workflows for consistent PHI handling.
- Compliance officer and committee: Assign accountability to oversee compliance and drive continuous improvement.
- Role-based training and education: Provide regular training to equip staff with practical HIPAA knowledge and reduce risks.
- Open communication channels: Enable anonymous reporting to encourage transparency and strengthen compliance culture.
- Monitoring and auditing: Conduct audits regularly to identify gaps and verify adherence to HIPAA standards.
- Enforcement and discipline: Apply consistent enforcement to ensure accountability and prevent non-compliance.
- Quick response and corrective action: Respond rapidly to incidents and implement measures to prevent recurrence.
Why HIPAA-compliance matters in customer service
To strengthen organizational performance, every healthcare brand must understand how privacy protection shapes business outcomes.
These principles drive how data is managed and secured, boosting operational reliability, enhancing customer confidence, and reducing exposure across healthcare and digital environments.
- Strengthens organizational performance: Reliable protection practices minimize mistakes and create smoother workflows, increasing speed, empathy, and the quality of every customer interaction.
- Maintaining patient trust: People expect their information to be safe. Any breach damages customer loyalty and weakens relationships that require significant effort to rebuild.
- Protects financial and brand stability: Non‑compliance leads to major fines and legal challenges, disrupting financial health and threatening the organization’s industry reputation.
- Reinforces ethical business standards: Beyond regulations, protecting privacy signals a commitment to doing what’s right, supporting long‑term credibility and responsible care.
- Improves operational consistency: Embedding strong privacy practices into customer service creates clear, repeatable processes. This reduces errors and elevates the overall customer experience.
6 Common HIPAA violations in customer service
Despite HIPAA’s strict standards, customer support teams may unintentionally violate rules due to human error or insufficient privacy training.
Understanding frequent HIPAA violations helps customer service professionals avoid mistakes that could compromise patient privacy and lead to regulatory penalties.

Unauthorized access/disclosure of PHI
Customer service staff may access or share patient information without valid reasons, violating HIPAA and risking serious privacy breaches.
This includes discussing patient issues publicly, accessing family records improperly, or accidentally revealing PHI to individuals without proper authorization.
Lack of proper training
Customer service training lacking HIPAA protocols may mishandle PHI, leading to unintentional breaches and a loss of patient trust.
Inadequate security measures
Customer service management lacking strong safeguards, technical, administrative, and physical, can expose PHI to unauthorized access or cyber threats.
According to a recent study published by JAMA Network, 81% of HIPAA-reported breaches in 2024 were attributed to hacking or IT-related incidents.
Examples include using unsecured email, weak passwords, or storing sensitive documents in areas accessible to unauthorized personnel, such as customer service representatives.
Failure to implement business associate agreements (BAAs)
Customer service teams working with vendors must ensure BAAs exist to prevent indirect HIPAA violations through third-party data handling.
Improper disposal of PHI
Customer service departments must securely dispose of PHI; improper shredding or deletion can lead to unauthorized access and data breaches.
Lost or stolen devices
Customer service staff losing unencrypted devices containing PHI can trigger HIPAA violations and compromise patient confidentiality.
How to prevent HIPAA violations in customer service
Preventing HIPAA violations requires a proactive approach, combining strong prevention measures with a clear incident response plan.
Strengthening data security and lowering breach risks starts with consistent privacy practices embedded across all customer support operations.
To enhance protection and reduce exposure, organizations should adopt these essential best practices for preventing HIPAA violations:
- Comprehensive training: Regularly educate staff, especially customer service teams, on HIPAA requirements, safe data handling, and how to recognize possible breaches.
- Access controls: Implement strict, role‑based access to PHI so only authorized personnel can view or modify sensitive information, reducing unnecessary access points.
- Encryption: Encrypted support systems protect PHI in transit and at rest, a requirement to pass HIPAA Security Rule audits and reduce exposure to data breaches and regulatory penalties.
- Secure communication channels: Require controlled, encrypted channels for all patient interactions to prevent unauthorized disclosure.
- Secure, HIPAA‑aligned systems: Ensure platforms used for storing, sharing, or processing PHI follow required administrative, physical, and technical safeguards to support secure workflows.
- Business associate agreements (BAAs): Require all third‑party vendors handling PHI to sign BAAs, which formalize their responsibility to protect patient data and support compliant integrations.
- Regular risk assessments: Conduct periodic assessments to uncover vulnerabilities and implement corrective actions across systems and processes.
- Policies and procedures: Establish and enforce clear, written guidelines for handling PHI, covering data entry, secure usage, sharing, retention, and disposal.
Incident response during breaches
Despite strong controls, breaches may still occur. A structured response plan minimizes disruption and preserves trust.
- Detection and identification: Early detection prevents escalation, supported by monitoring tools and audits.
- Containment and eradication: Isolate affected systems and remove threats to limit exposure.
- Recovery and notification: Restore operations and notify affected parties promptly to maintain transparency.
- Documentation and review: Record incident details and update policies to prevent recurrence.
Choosing the right HIPAA-compliant support system
Selecting a support system for healthcare environments requires more than basic security.
Any platform that handles patient inquiries, service requests, or sensitive communications must comply with HIPAA privacy and security requirements.
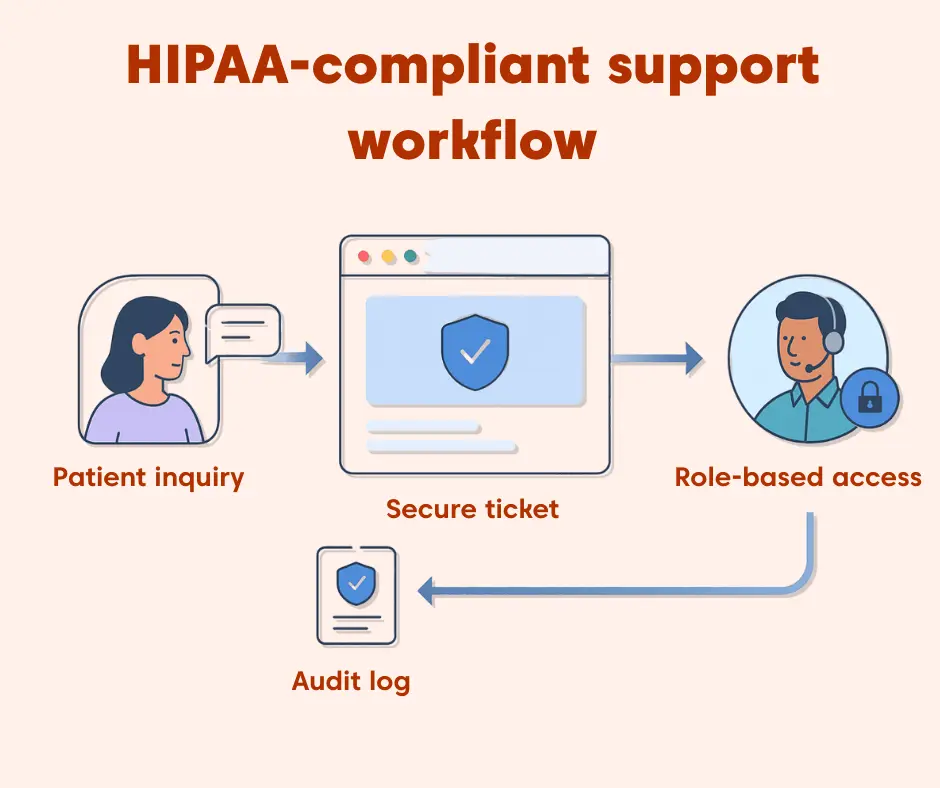
When evaluating a HIPAA-compliant support system, healthcare organizations should focus on these core capabilities:
- Data encryption: Ensure PHI is encrypted both in transit and at rest to protect sensitive data during communication, storage, and processing.
- Access controls: Use role-based permissions so only authorized users can view or modify PHI, reducing the risk of internal misuse or accidental exposure.
- Audit logs: Maintain detailed records of who accessed PHI, when changes occurred, and what actions were taken to support audits and investigations.
- Secure communication: Enable secure channels for patient messages, attachments, and internal notes without relying on unsecured email or messaging tools.
- Business Associate Agreements (BAAs): Any vendor that handles PHI must sign a BAA to formally acknowledge responsibility for HIPAA-compliant data protection.
Evaluating these requirements early helps healthcare teams reduce compliance risks, improve operational consistency, and ensure patient information remains protected throughout the support lifecycle.
For teams assessing support software, refer to our detailed guide on HIPAA-compliant ticketing systems.
Staying HIPAA-compliance: Your path to ethical and secure support services
HIPAA-compliance is more than a regulatory requirement it is a foundational commitment to protecting patient privacy and maintaining trust in healthcare interactions.
Upgrading to a HIPAA‑compliant help desk system or refining existing workflows to align with HIPAA safeguards helps support teams operate more securely, respond faster.
It also reduces risk and ensures the organization stays prepared as compliance requirements continue to evolve.
For support teams aiming to simplify compliance while still delivering a high‑quality service experience, tools like BoldDesk can help streamline workflows, safeguard PHI.
They also provide a reliable framework for continuous HIPAA readiness, ensuring teams stay compliant as processes and standards evolve.
Did this guide help clarify how HIPAA affects customer support in healthcare? Share questions or feedback in the comments. We’re here to support you.
Related articles
Frequently asked question
Covered entities include healthcare providers, health plans, and healthcare clearinghouses that electronically transmit health information in any HIPAA‑regulated transaction. These organizations must follow all HIPAA Privacy and Security Rule requirements to protect PHI from unauthorized access.
Business associates are any third‑party vendors or individuals who create, receive, maintain, or transmit PHI on behalf of a covered entity. This includes billing companies, IT service providers, cloud storage vendors, data processors, consultants, and subcontractors. They are required to sign a Business Associate Agreement (BAA) and follow the relevant HIPAA privacy and security provisions.
Yes. if a cloud service stores, processes, or transmits PHI, they must implement administrative, physical, and technical safeguards to meet HIPAA requirements. They must sign a BAA and implement Security Rule safeguards such as encryption, access controls, and breach‑notification procedures to ensure PHI remains protected.
HIPAA requires covered entities and business associates to implement administrative, physical, and technical safeguards to protect ePHI. These include:
- Encryption of PHI
- Role‑based access controls
- Workforce training
- Audit logs and activity monitoring
- Regular risk analysis and risk management
These measures help maintain the confidentiality, integrity, and availability of ePHI.
Yes. Telehealth services must fully comply with HIPAA Privacy, Security, and Breach Notification Rules. Providers must use HIPAA‑compliant platforms, ensure encryption, verify identity, protect session privacy, and use vendors who will sign BAAs. OCR provides additional guidance for audio‑only and video telehealth to help providers reduce privacy and security risks.